Menandmice 9 Ways To Mitigate Ddos Attacks
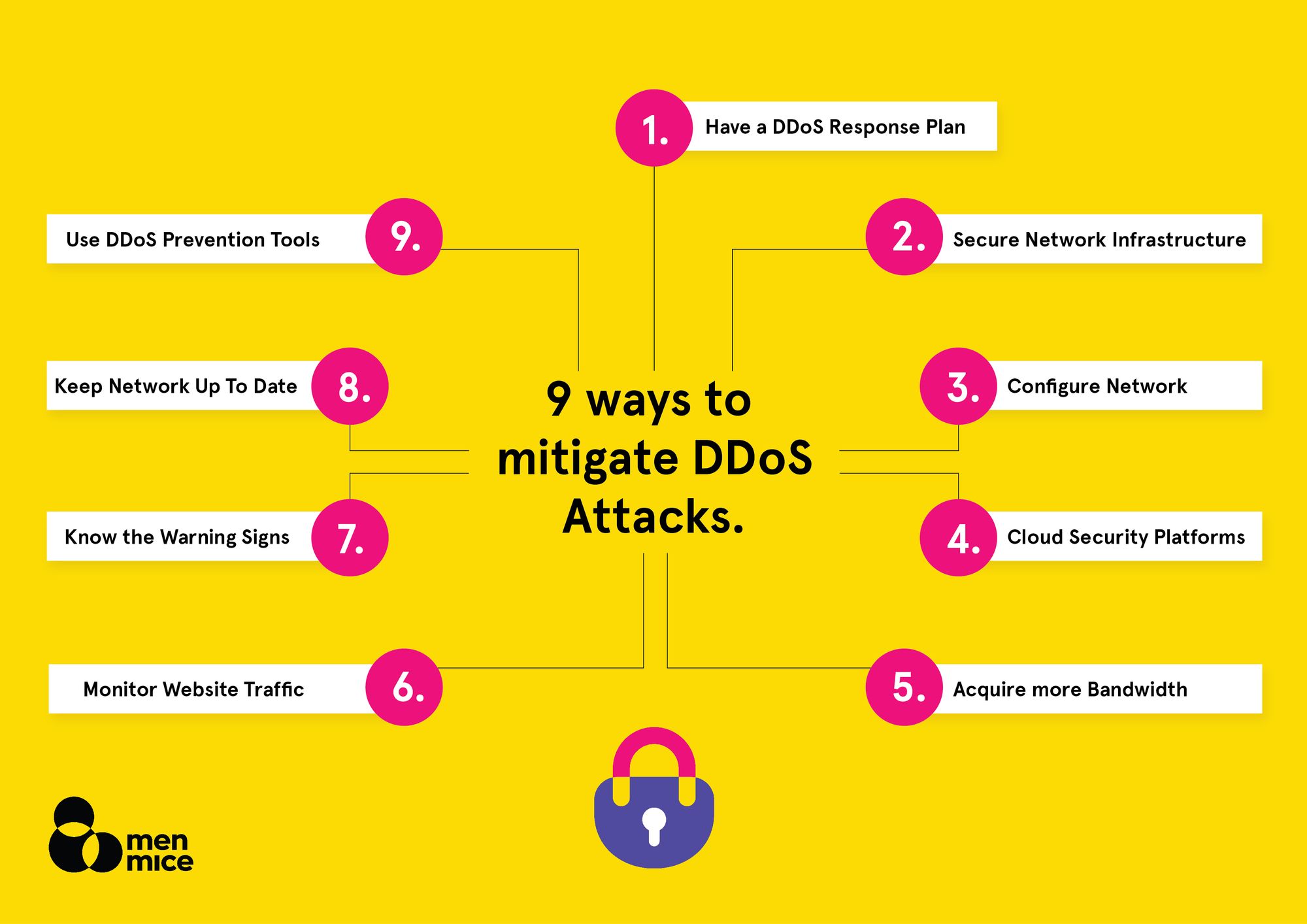
Menandmice 9 Ways To Mitigate Ddos Attacks
If this picture is your intelectual property (copyright infringement) or child pornography / immature images, please Contact Us for abuse. We will follow up your report/abuse within 24 hours.
Related Images of what is a ddos attack how to protect your network from hackers
What Is A Ddos Attack How To Protect Your Network From Hackers
What Is A Ddos Attack How To Protect Your Network From Hackers
Ddos Attacks A Guide Ddos Attack Protection Tips Norton
Ddos Attacks A Guide Ddos Attack Protection Tips Norton
A Beginners Guide To Understanding Ddos Attacks And How To Protect Your
A Beginners Guide To Understanding Ddos Attacks And How To Protect Your
Ddos Attacks A Guide Ddos Attack Protection Tips Norton
Ddos Attacks A Guide Ddos Attack Protection Tips Norton
A Beginners Guide To Ddos Attacks And How To Protect Your Site
A Beginners Guide To Ddos Attacks And How To Protect Your Site
What Is A Ddos Attack And How Do Ddos Attacks Work
What Is A Ddos Attack And How Do Ddos Attacks Work
What Is A Ddos Attack And How Do Ddos Attacks Work Vpnmentor
What Is A Ddos Attack And How Do Ddos Attacks Work Vpnmentor
How To Prevent Your Data From Being Hacked Infographic Digital
How To Prevent Your Data From Being Hacked Infographic Digital
Everything You Need To Know About Ddos What Is A Ddos Attack Dzone
Everything You Need To Know About Ddos What Is A Ddos Attack Dzone
How To Protect Your Computer From Hackers Ultimate Guide
How To Protect Your Computer From Hackers Ultimate Guide
What Is A Ddos Attack How To Protect Your Network From Hackers
What Is A Ddos Attack How To Protect Your Network From Hackers
How To Stop Ddos Attack How To Prevent Ddos Attacks Indusface Blog
How To Stop Ddos Attack How To Prevent Ddos Attacks Indusface Blog
What Is Ddos How To Protect Your Network From It Ultahost Blog
What Is Ddos How To Protect Your Network From It Ultahost Blog
How To Protect Firewalls From Hacking Managed Cyber Security
How To Protect Firewalls From Hacking Managed Cyber Security
How To Protect Yourself Against Hackers Technology Compute
How To Protect Yourself Against Hackers Technology Compute
How To Protect Your Network From Protocol Based Ddos Attacks
How To Protect Your Network From Protocol Based Ddos Attacks
Ddos Proxy Protection Best Ddos Protection Of 2021
Ddos Proxy Protection Best Ddos Protection Of 2021
How To Protect Your Computer From Hackers Ultimate Guide
How To Protect Your Computer From Hackers Ultimate Guide
Everything You Need To Know About Cybersecurity Attacks And How To
Everything You Need To Know About Cybersecurity Attacks And How To
Wordpress Ddos Attack Tips To Protect And Secure Your Website
Wordpress Ddos Attack Tips To Protect And Secure Your Website
Top 10 Best Ddos Protection Services To Secure Your Website
Top 10 Best Ddos Protection Services To Secure Your Website
Exploring Network Security 8 Ways To Protect Your Network
Exploring Network Security 8 Ways To Protect Your Network
5 Ways To Protect Your Network Systems From Remote Workers
5 Ways To Protect Your Network Systems From Remote Workers
How To Protect Your Network From Protocol Based Ddos Attacks
How To Protect Your Network From Protocol Based Ddos Attacks
How To Protect Successfully Your Network Against Ddos Attacks 5 Steps
How To Protect Successfully Your Network Against Ddos Attacks 5 Steps
9 Ways To Protect Your Business From Cyber Attacks
9 Ways To Protect Your Business From Cyber Attacks