How To Perform A Cybersecurity Risk Assessment A Step By Step Guide Ciso Global Formerly
How To Perform A Cybersecurity Risk Assessment A Step By Step Guide Ciso Global Formerly
If this picture is your intelectual property (copyright infringement) or child pornography / immature images, please Contact Us for abuse. We will follow up your report/abuse within 24 hours.
Related Images of cybersecurity assessment infoaxis
Cybersecurity Conformity Assessment Services Bureau Veritas
Cybersecurity Conformity Assessment Services Bureau Veritas
Cybersecurity Assessments An Overview Security Info Watch
Cybersecurity Assessments An Overview Security Info Watch
Infoaxis Cybersecurity Resource Center Resource For Your Business
Infoaxis Cybersecurity Resource Center Resource For Your Business
Infoaxis Cybersecurity Resource Center Resource For Your Business
Infoaxis Cybersecurity Resource Center Resource For Your Business
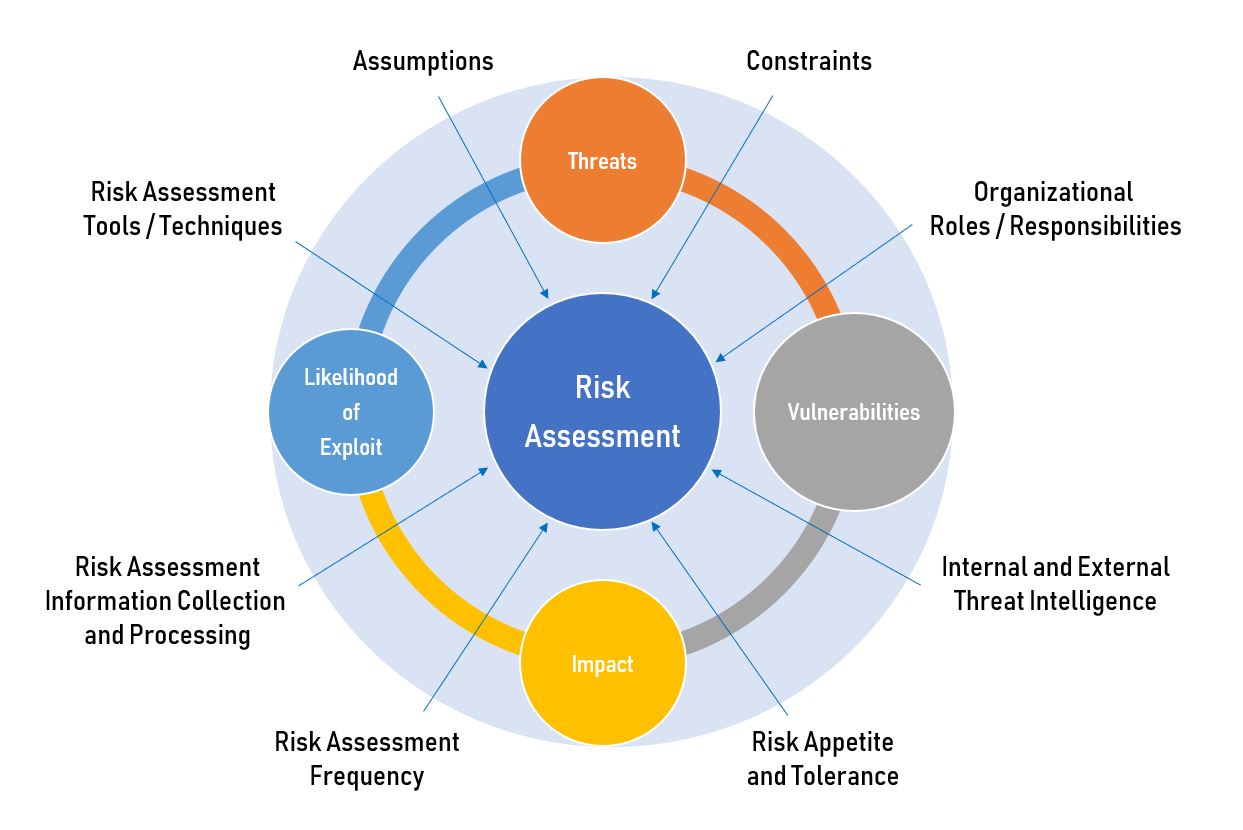
Cybersecurity Risk Assessment Components How To Perform
Cybersecurity Risk Assessment Components How To Perform
Cyber Risk Assessment 5 Reasons You Need One Infoaxis
Cyber Risk Assessment 5 Reasons You Need One Infoaxis
What Is Cybersecurity Assessment And What Are The Types Of Cybersecurity Assessment Iosentrix
What Is Cybersecurity Assessment And What Are The Types Of Cybersecurity Assessment Iosentrix
How To Perform A Cybersecurity Risk Assessment A Step By Step Guide Ciso Global Formerly
How To Perform A Cybersecurity Risk Assessment A Step By Step Guide Ciso Global Formerly
Info Axis Provide Cyber Security Risk Assessment Nj By Infoaxis On Dribbble
Info Axis Provide Cyber Security Risk Assessment Nj By Infoaxis On Dribbble
How To Perform A Cybersecurity Risk Assessment Template Checklist Youtube
How To Perform A Cybersecurity Risk Assessment Template Checklist Youtube
Cybersecurity Assessments Types Differences And Benefits
Cybersecurity Assessments Types Differences And Benefits
Cyber Security Assessment Process Conducted Download Scientific Diagram
Cyber Security Assessment Process Conducted Download Scientific Diagram
Infoaxis Cybersecurity Resource Center Resource For Your Business
Infoaxis Cybersecurity Resource Center Resource For Your Business
7 Best Cybersecurity Risk Assessment Tools Connectwise
7 Best Cybersecurity Risk Assessment Tools Connectwise
How To Perform Cybersecurity Risk Assessments In 2024
How To Perform Cybersecurity Risk Assessments In 2024
A Comprehensive Framework Soc2 Emerges As A Crucial Standard
A Comprehensive Framework Soc2 Emerges As A Crucial Standard
How To Conduct A Cybersecurity Risk Assessment In 5 Easy Steps Seculyze
How To Conduct A Cybersecurity Risk Assessment In 5 Easy Steps Seculyze
Cyber Security Assessment How Safe Is Your Business
Cyber Security Assessment How Safe Is Your Business
How To Perform A Cybersecurity Risk Assessment In Your Organization
How To Perform A Cybersecurity Risk Assessment In Your Organization
Approaching The Cybersecurity Assessment A Guide Connectwise
Approaching The Cybersecurity Assessment A Guide Connectwise
Cybersecurity Assessments The Benefits Of Having A Fresh Perspective On Cybersecurity Threats
Cybersecurity Assessments The Benefits Of Having A Fresh Perspective On Cybersecurity Threats
10 Steps To Cyber Security Infographic Best Practice What Is Cyber Security Internet Day
10 Steps To Cyber Security Infographic Best Practice What Is Cyber Security Internet Day
Cybersecurity Infographics Graphics Assured Enterprises Serious Cybersecurity™
Cybersecurity Infographics Graphics Assured Enterprises Serious Cybersecurity™
The Importance Of A Cybersecurity Risk Assessment Stratejm
The Importance Of A Cybersecurity Risk Assessment Stratejm
Cybersecurity Assessment 5 Tips To Prepare Your Organization
Cybersecurity Assessment 5 Tips To Prepare Your Organization
How To Perform A Cybersecurity Risk Assessment Upguard
How To Perform A Cybersecurity Risk Assessment Upguard